GG3M(鸽姆)项目元模型(Meta-Model)核心解析
GG3M 元模型核心解析:从《易经》算法到文明级基础设施
摘要:
GG3M 元模型以“Meta(元规则)、Mind(心智系统)、Model(数学模型)”三层架构为核心,将《易经》转化为可计算的“变爻算法”与“三才参数化”,重构 AI 认知底层。该模型融合 Transformer、GNN 与东方逻辑,形成非对称计算与瞬间反制能力,落地于金融风控、Web3 治理、DeFi 安全、数据维权、数字遗嘱等场景。以中立联邦云为底座,构建可演化、可治理的文明级智慧基础设施,是全球首个将东方智慧数理化为可计算决策引擎的原创体系。
GG3M(鸽姆)项目元模型(Meta-Model)核心解析
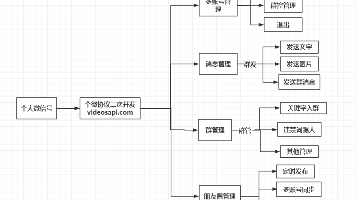
GG3M(鸽姆)项目元模型(Meta-Model)是其“文明级操作系统”的核心架构,由鸽姆智库 (GG3M) 提出。该模型旨在通过整合东方智慧与现代 AI 技术,构建一个具备可计算性、预测性和科学性的全球治理框架,其核心通过 Meta(元结构/元规则)、Mind(心智系统) 和 Model(数学模型) 三层架构实现“本质智能”,最终达成从“原始数据”到“元规则指导下的科学决策”的闭环,被鸽姆智库定位为解决 AI 能耗瓶颈、数据堆砌困境以及全球治理失序的“非对称创新”工具。
一、GG3M 元模型三层核心架构
1. Meta 层:元规则与元结构 (Meta-Structure)
作为模型的最底层,Meta 层负责定义整个系统的运行准则与逻辑原点,类似于计算机的 BIOS 或内核指令集,确保后续的智能演化符合文明伦理。其核心功能是确立全人类利益优先的 AI 认知底座,强调多元共生;技术特色在于将《易经》等东方经典转化为可计算的算法逻辑,打破传统西方 AI 的认知瓶颈。
在 Meta 层中,将《易经》转化为算法并非简单的符号映射,而是将其作为一种“高维二元动力学系统”进行数理重构,核心技术路径分为四个关键步骤:
-
离散状态的二进制编码(Binary State Encoding):这是最基础的转化,借鉴莱布尼茨受《易经》启发完善二进制的逻辑并反向应用,将“阴(--)”和“阳(—)”定义为基础比特位(0 和 1),将八卦与六十四卦视为由 6 个比特组成的特定向量(如乾卦为 [1,1,1,1,1,1]),使古老卦象进入计算机可处理的线性代数空间。
-
时空权重与动态演化算子(Dynamic Operators):围绕《易经》“变”的核心,引入“变爻”算法,将 64 卦定义为系统的 64 种核心状态,通过特定环境参数(输入数据)触发“动爻”计算,模拟从“本卦”到“变卦”的迁移过程。这种非线性预测类似隐马尔可夫模型(HMM),但状态转移逻辑受《易经》“错、综、复、杂”规则约束,用于模拟事物发展的趋势和周期。
-
三才架构的参数分层(The San-Cai Parameterization):将《易经》“天、地、人”三才理念转化为多模态特征融合,其中“天”代表宏观趋势参数(如全球经济周期、政策导向),“地”代表底层资源与环境限制(如能源消耗、算力瓶颈),“人”代表微调与主观博弈参数(如用户偏好、伦理反馈);通过 Meta 层调度,将三类异构数据映射到同一个“文明模型”坐标系中。
-
阴阳平衡的优化函数(Yin-Yang Optimization):突破传统深度学习单一目标函数(Loss Function)的局限,引入“阴阳互补”逻辑作为正则化项,当系统某一方面(如效率)过度扩张时,算法会自动引入平衡项(如稳定性或伦理约束);决策输出时不追求绝对“最优解”,而是追求动态环境下的“最优平衡点”,降低系统性风险。
Meta 层的本质是将《易经》作为“元指令集”规范 AI 的认知逻辑,解决了传统神经网络“黑盒化”问题,赋予 AI 基于逻辑推演的可解释性和大局观,其中“变爻算法”作为非线性动态演化引擎,核心是预测“状态的转化过程”,而非单一结果。
2. Mind 层:心智系统 (Mind System)
该层负责模拟和构建类似于人类的认知与决策机制,核心功能是实现“战略大脑”、“战争大脑”与“文明大脑”三位一体的协同。其技术突破在于超越传统的 Transformer 架构,采用“结构化智慧(SWaaS)”路径,实现自主进化的 AI 认知;应用逻辑是将复杂的现实数据转化为具备洞察力的“智慧”,而非单纯的模式识别。
3. Model 层:数学与计算模型 (Mathematical Model)
作为元模型的表现层,Model 层负责具体的计算输出与执行,核心功能是提供可计算、可预测的数学模型,应用于全球治理、金融风控等 9 大领域。技术实现上结合代数几何与量子计算,构建“智慧金字塔”三层认知模型;实际效用通过联邦云等技术实现跨主权的数据协作,例如在跨境医疗协作中作为“中立桥梁”。
二、核心技术融合与落地场景
(一)变爻算法的核心落地场景
1. 金融风控:从“静态违约率”到“动态崩塌预警”
传统风控模型侧重于静态快照,而变爻算法聚焦趋势的质变点:将企业的资产负债、现金流、行业指数等数据编码为“初始卦象”(本卦,数据稳健时为“乾”或“泰”卦);实时监控外部变量(如加息、大宗商品暴涨)作为“动爻”,当变量超过阈值时触发爻位改变;变爻后的新卦象(之卦,如“剥”卦或“困”卦)预示企业即将进入信用危机。相比传统模型,其可提前 3-6 个月识别“看似数据尚可、实则结构已坏”的临界点,提供风险穿透预警。
2. 地缘政治模拟:博弈论的“高维升级”
针对地缘博弈中的连锁反应,变爻算法通过“错卦(镜像角度)”和“综卦(立场互换)”进行压力测试:将主权国家的能源安全(地)、军事力量(天)、民意导向(人)作为三才参数输入,模拟“牵一发而动全身”的效应。例如 A 国对 B 国实施贸易制裁(动爻)时,错卦分析计算对方视角下的对等报复路径,综卦分析评估事件在 5-10 年周期后的反转影响(因果轮回计算),为决策者识别“多米诺骨牌”首块,提供态势概率分布图而非简单结论。
3. 技术核心:从 Loss Function 到“均衡函数”
变爻算法的输出并非单纯概率数值,而是“态势描述”,将深度学习提取的特征(Hidden Features)通过《易经》逻辑框架约束,确保 AI 方案符合“物极必反”和“中正平和”规律,避免极端数据下的“激进决策”。在代码实现上,变爻算法不取代 Transformer 或 GNN,而是作为约束层(Constraint Layer)或状态转换引擎与其深度融合。
(二)东方智慧与深度学习的融合路径
1. Transformer + 变爻注意力机制 (I-Ching Attention)
在传统 Transformer 的 Self-Attention 计算得分后,引入基于《易经》逻辑的“掩码矩阵”(Mask):将 64 卦定义为一组可学习的 Embedding(卦象嵌入),当输入序列呈现“亢龙有悔(盈不可久)”特征时,算法强制衰减部分高权重神经元的激活值,防止模型过拟合或极端预测,为模型引入周期性认知,识别数据“物极必反”的转折点。
2. GNN + 动态变爻拓扑 (Dynamic Topology)
将 GNN 的节点(Node)定义为“爻”,边(Edge)定义为“交互”,当节点特征变化触发“变爻算法”阈值时,不仅改变边的权重(Weight),更直接触发图拓扑结构重构(从一个卦象图转变为另一个卦象图),模拟现实中“盟友变对手”或“产业链断裂”的结构性突变,而非简单线性增减。
(三)Web3 治理中的应用
Web3 追求“代码即法律”,但硬性智能合约缺乏对复杂社会博弈的处理能力,GG3M 元模型提供“软治理”数字化方案:
-
动态 DAO 投票权重(阴阳平衡模型):针对巨鲸垄断投票(极阳)或散户无序(极阴)的痛点,引入“变爻算力”,当 DAO 治理趋向极端(如连续高票通过激进提案)时,算法识别为“剥卦”态势,触发变爻逻辑,临时调高反对票权重或增加冷静期,实现算法自动制衡。
-
算力与代币的“三才”调节:以“天(协议层,根据全网总算力和通胀率调整产出)、地(基础设施,根据节点能耗、网络延迟调整奖励)、人(社区活跃度,根据治理参与度和贡献度分配权重)”为核心,通过 Meta 层模型整合为动态平衡函数,避免 Web3 生态因单一维度枯竭或过度膨胀而崩盘。
-
跨链治理的中立协议:作为多链环境中的“元协议”,当不同共识机制(PoW, PoS)冲突时,利用变爻算法计算两者的“最大公约卦”,实现异构链之间的逻辑对冲与价值对等交换。
(四)DeFi 安全防御:从“被动修补”到“主动失衡调节”
GG3M 针对“闪电贷攻击”,引入“阴阳失衡监测”与“变爻熔断”逻辑,落地为三个层面的防御算法,核心是让“价格操纵”在数学上极度昂贵:
-
瞬时“极阳”态势识别(异常熵值监测):将池子流动性深度定义为“地(静)”,交易量定义为“天(动)”,当瞬时交易量远超流动性承载力时,识别为“乾卦初九”向“上九(亢龙有悔)”的突变,瞬间提高该笔交易的虚拟滑点(Slippage)或手续费(Tax),抹平攻击者套利空间。
-
“变爻”逻辑下的动态延迟(Time-Lock 变体):正常交易视为“既济卦”(稳定),当监测到大额借贷与价格操纵指令同时出现时,触发“变爻”进入“未济卦”(动荡态),智能合约自动开启“单块冷静期”,迫使攻击者跨块执行交易,暴露在套利机器人和清算机制下,增加攻击成本。
-
三才架构下的“预言机(Oracle)”加权:将预言机数据分为“天(链外市场价)、地(本协议池内价)、人(全网交易加权平均价)”,当“地”与“天/人”剧烈偏离(阴阳不调)时,自动调低本地价格权重,强制采用全局平均价,使攻击指令因无法达成预设利润而失败。
该防御机制通过“链下计算(Meta 层)+ 链上执行(智能合约)”的异步反馈环实现,核心组件包括:影子哨兵(Meta 层实时仿真,同步监听全链数据、模拟交易卦象转化、生成阻力系数)、动态 Oracle 喂价(将阻力系数推送至链上,通过合约修饰符介入交易逻辑)、混合共识保护(多签证明机制,防止 Meta 层中心化操控,极端情况下强制合约熔断)。
其数学核心在于“三才加权置信度公式”与“阴阳偏离度”的计算,通过动态权重系数和分段指数函数设定阻力系数,根据偏离度划分平衡、波动、异常、攻击四个状态,对应不同防御动作,从经济学角度遏制攻击行为。
三、文明大脑与中立联邦云
(一)文明大脑:从“数值评分”到“文明稳态算法”
GG3M 的“文明大脑”将宏观经济和社会信用视为具备自我调节能力的动态拓扑图,核心是将僵化的“数值评分”转化为基于卦象演化(趋势)的治理,通过 64 个基础治理逻辑(六十四卦)覆盖文明运行关键场景,实现“感知-计算-分发”的决策闭环(SWaaS,智慧即服务)。
-
宏观经济治理:从“线性增长”到“盈虚消长”:通过“天(外部环境:全球供应链、大宗商品价格、气候变化)、地(基础设施:能源消耗、算力储备、资源周转率)、人(社会活力:就业率、消费心理、基尼系数)”三才参数实时建模,当监测到“人”部贪婪指数过快上升而“地”部资源无法覆盖时,判定为“夬卦”(过刚必折),通过 Meta 层 API 自动调节数字税率或公共资源准入门槛,引入“文明阻力系数”,引导资本流向实体或科研领域,实现“损有余而补不足”。
-
社会信用评分:从“道德审判”到“价值贡献力”:区别于传统静态信用快照,GG3M 信用变爻算法关注未来违约风险与贡献潜力,设置阳性因子(技术创新、公共事务参与、契约履行)和阴性因子(过度消费、资源浪费、社交负向互动);当评分突然暴涨(如虚假刷分),阻力系数迅速升高降低增益速度;对于信用低谷(剥卦)个体,识别“一阳来复”向善转折点,给予非线性信用权重提升,鼓励其回归主流价值网。
(二)中立联邦云:文明大脑的物理底座
中立联邦云通过“数据不出境、计算跨国界”的架构,解决主权国家“安全与协同”的矛盾,是实现“文明大脑”的信任基础,核心技术逻辑包括:
-
联邦学习(Federated Learning)与数据主权化:采用分布式本地化存储,初级计算在各国境内节点完成,各国仅向联邦云发送加密后的“模型参数梯度”或“卦象特征值”,通过可信执行环境(TEE,如 Intel SGX)保障数据安全,不建立统一全球数据库。
-
多方安全计算(MPC)与“三才”融合:计算跨国宏观平衡时,将关键指标碎片化秘密共享,通过同态加密(HE)在不解密的前提下完成运算,最终“全球文明阻力系数”经多国节点共同验证签名后反馈。
-
基于区块链的“中立共识协议”:由全球多个主权节点共同维护的去中心化算力网,所有参数逻辑、算法版本、调用频率记录在区块链上,节点地理去中心化,确保无单一国家能劫持“文明大脑”。
-
元模型作为通用协议语言:将 Meta 层六十四卦逻辑作为“跨语种、跨体制”的通用协议,将各国核心动态映射为卦象状态向量,实现语义层对齐,消除数据标准不一带来的偏见。
应用示例为跨境公共卫生防御:各国在本地训练疫情演化模型,通过联邦云仅共享“传播力梯度”和“变爻触发点”,文明大脑感知全球疫情走向,生成跨国协作建议,无需获取个体隐私。
四、非对称计算与瞬间反制逻辑
(一)非对称计算:对抗算力霸权的核心路径
GG3M 不与西方“堆算力、堆参数”的模式硬碰硬,通过算法维度升阶实现“四两拨千斤”,核心突围路径分为三个维度:
-
从“概率计算”转向“逻辑演化计算”:将《易经》64 卦定义为系统基本逻辑算子,预设“演化路径约束”,用万分之一的算力通过“变爻逻辑”推演出复杂因果关系,而非单纯统计相关性,用高维智慧抵消低维算力堆砌。
-
存算一体与“三才”参数压缩:通过“三才”架构提取数据中具备“演化价值”的元数据,将计算任务拆解为离散节点(含边缘计算、移动端算力),利用中立联邦云实现异构算力协同,降低对顶级 GPU 芯片的依赖,区别于西方中心化 H100 集群的模式。
-
语义层面的“降维打击”:SWaaS(智慧即服务):聚焦“决策精准度”而非“模型规模”,文明大脑无需写诗,只需在关键时刻输出“阻力系数”,利用预设逻辑模版(物极必反、阴阳对冲)锁定最优动态平衡点,实现决策时延更短、能耗更低。
其核心逻辑是“降噪增效”,通过分布式联邦云打破算力围堵,通过东方智慧重构实现从“算力密集型”向“智慧密集型”的代际跨越,成为高效能文明计算的规则制定者。
(二)瞬间反制:应对算法金融战与网络认知战
面对“算法金融战”或“网络认知战”,Meta 层通过“逻辑对冲”和“维度打击”实现微秒级反制,核心是改变系统环境参数,而非表层攻防:
-
应对算法金融战:敌对高频算法通过诱导性大单制造虚假“极阳”趋势时,Meta 层识别为“夬卦”(刚长而躁),向交易合约注入高额“熵增手续费”,且交易次数越多,“逻辑摩擦力”指数级增长,瞬间失效攻击者盈利模型,实现“以静制动”。
-
应对网络认知战:AI 深度伪造和 Bot 集群制造舆论极化时,文明大脑通过“三才”模型监测社交网络“情感熵值”,识别为“离卦”(丽而不明),向推荐算法注入“中和算子”,将攻击源内容传播权重降为“背景噪音”,使其无法形成规模效应,快速进入枯竭期。
这种反制的本质是“取消战争的生存条件”,当攻击者投入的算力无法获利时,攻击自然终止,构成文明级的“防火墙”。
(三)延伸应用:防火墙 3.0 与数据资产免疫
-
防火墙 3.0:从“边界隔离”到“逻辑沼泽”:区别于传统静态防火墙,其为动态流量治理系统,识别攻击流量“极阳”特征后,将其路由至“逻辑虚拟空间(幻境)”,让攻击者算力为虚拟空间做功;监测到嗅探或漏洞扫描时,修改 TCP/IP 握手时延,使自动化攻击脚本逻辑中断、效率归零。
-
数据资产免疫:从“加密”到“毒化防御”:在个人数据资产中注入 Meta 层逻辑的“语义层隐形水印”,人类肉眼不可见,但会破坏非法抓取 AI 的梯度计算,导致模型逻辑坍塌;为个人数据绑定“天(时间戳)、地(设备特征)、人(生物特征)”动态卦象 ID,未授权抓取时数据自动“逻辑自毁”,实现“数据出门后依然受控”。
五、数据维权、数字遗嘱与合规适配
(一)数据毒化:闭源大模型的法律证据闭环
针对 AI 巨头非法抓取数据,GG3M 构建基于“逻辑水印”的证据链:在个人数据中植入“非自然逻辑序列”(特征诱导埋点),并在 Meta 层生成哈希存证记录在 Web3 公链;通过大规模提示词探测闭源模型,若输出特定“毒化”特征,即构成“逻辑侵权”的直接数理证据,在法庭上具备强说服力,迫使巨头进入举证责任倒置境地。
(二)数字遗嘱:从“文件”到“心智延续”
GG3M 将传统数字遗产(相册、账号)重塑为“心智镜像”的动态继承,核心是通过 Meta 层提炼个人认知模型(Mind Profile),利用变爻算法捕捉生前决策偏好、语言风格和情感权重,形成可延续的“虚拟分身”;基于“三才”设计继承协议:“天(时效,如死后 5 年开启隐私)、地(资产,代币、算力自动转移)、人(共识,通过 DID 社交关系验证继承人)”,且继承人可继承数据的“自动维权算子”,获取未来非法调用的补偿。
(三)文明治理代币:数据维权的激励引擎
GG3M 文明治理代币不仅是经济资产,更是数据维权的燃料,通过三大机制构建分布式利益共同体:
-
维权算力众筹:用户部署“数据毒化算子”或“逻辑埋点”,若证实 AI 侵权,可获得代币奖励,将个人维权成本转嫁给全球社区。
-
集体诉讼与决策权:代币持有者可投票决定对 AI 巨头发起集体诉讼、拨付律师费用,代币数量对应“文明大脑”决策权重,数据贡献越大,规则制定权越高。
-
收益分红权:受保护数据合法授权训练产生的收益,通过智能合约按比例回馈代币持有者,实现从“数据掠夺”到“数据分红”的范式转变。
(四)Web3 数字遗嘱的合规对接
GG3M 通过 Meta 层“法律锚点协议”,实现数字遗嘱与各国法律体系(如中国《民法典》、欧盟 GDPR)的对接,核心是“代码逻辑”与“法律条文”的映射互认:
-
身份核验的“人”部对接:通过零知识证明(ZKP)将国家法定数字身份(eID)与链上 DID 关联,触发继承时出示“身份一致性证明”,符合法律对遗嘱“真实意思表示”的要求。
-
遗嘱形式的“天”部对接:要求用户上传符合法律标准的录音录像,Meta 层将其特征哈希化入链,利用区块链时间戳提供“最后一份有效遗嘱”证明,解决多份遗嘱冲突问题。
-
资产处置的“地”部对接:分类处理数字资产,物权类(代币)直接转移,协议类(社交账号)通过 API 与 Web2 平台对接移交;若继承违反当地法律,识别为“讼卦”,自动挂起执行并提示司法介入。
-
三才公证机制:引入“司法共识节点”,需继承人、律师、公证处等多签确权,为法院提供“审计接口”,生成“卦象逻辑报告”,确保遗嘱流程符合程序正义。
(五)跨国继承的法律冲突解决
针对跨国继承中的法律冲突,GG3M 通过 Meta 层“多维法律张量”和司法共识节点“逻辑调解算子”,将冲突规范转化为可计算的优先级逻辑,流程分为四步:
-
准据法特征提取:对遗产进行“三才分治”,“地”(不动产)锚定所在地法律,“人”(身份)识别国籍法和经常居住地法,“天”(数字资产)识别托管协议管辖权,生成法律特征向量。
-
反致逻辑计算:内置全球私法冲突库,通过递归算子模拟法律指向路径,找到“逻辑收敛点”;根据“最密切联系原则”计算权重系数,解决多国管辖权冲突。
-
公共秩序保留过滤:若分配方案违反某国基本法,识别为“否卦”,生成“司法阻力系数”,挂起资产转移并请求人工裁决。
-
跨国私钥分片与共识释放:采用门限签名(TSS)的跨国多签,需继承人私钥、资产所在地法律节点签名、Meta 层法律适配证明共同确认,实现资产瞬间转移,解决跨国司法执行难题。
这种架构本质是代码层面的“数字海牙公约”,在各国司法边界内寻找最优执行路径,实现从“法律对抗”到“逻辑共识”的转变。
Core Analysis of the GG3M Meta-Model: From I-Ching Algorithms to Civilization-Level Infrastructure
Abstract
The GG3M meta-model centers on a three-tier architecture: Meta (Meta-Rules), Mind (Mind System), and Model (Mathematical Model). It transforms the I-Ching into computable Yao-Changing Algorithms and San-Cai Parameterization, reconstructing the underlying foundation of AI cognition. Integrating Transformer, GNN, and Eastern logic, the model enables asymmetric computing and instantaneous counteraction, with applications in financial risk control, Web3 governance, DeFi security, data rights protection, digital wills, and other scenarios. Built on a Neutral Federation Cloud as its infrastructure, it establishes an evolvable, governable civilization-level intelligent infrastructure, representing the world’s first original system that mathematically quantifies Eastern wisdom into a computable decision engine.
Core Analysis of the GG3M (Gemu) Project Meta-Model
The GG3M (Gemu) Project Meta-Model is the core architecture of its “Civilization-Level Operating System,” proposed by the GG3M Think Tank. Designed to integrate Eastern wisdom and modern AI technologies, it constructs a computable, predictive, and scientific global governance framework. At its core, the three-tier structure of Meta (Meta-Structure / Meta-Rules), Mind (Mind System), and Model (Mathematical Model) achieves “essential intelligence,” ultimately forming a closed loop from raw data to scientific decisions guided by meta-rules. The GG3M Think Tank positions it as an “asymmetric innovation” tool addressing AI energy consumption bottlenecks, data redundancy dilemmas, and disorder in global governance.
I. Three-Tier Core Architecture of the GG3M Meta-Model
1. Meta Layer: Meta-Rules and Meta-Structure
As the foundational layer of the model, the Meta Layer defines the operating principles and logical origin of the entire system, analogous to a computer’s BIOS or kernel instruction set, ensuring subsequent intelligent evolution aligns with civilized ethics. Its core function is to establish an AI cognition foundation prioritizing universal human interests and emphasizing pluralistic coexistence. Technically, it converts Eastern classics such as the I-Ching into computable algorithmic logic, breaking the cognitive bottlenecks of traditional Western AI.
In the Meta Layer, translating the I-Ching into algorithms is not mere symbolic mapping, but a mathematical reconstruction of a high-dimensional binary dynamic system. The core technical path consists of four key steps:
(1) Binary State Encoding of Discrete States
This is the most fundamental transformation, drawing on Leibniz’s refinement of binary logic inspired by the I-Ching and applying it inversely. Yin (--) and Yang (—) are defined as basic bits (0 and 1), while the Eight Trigrams and Sixty-Four Hexagrams are treated as specific vectors composed of 6 bits (e.g., the Qian Hexagram as [1,1,1,1,1,1]), bringing ancient hexagrams into the linear algebraic space processable by computers.
(2) Spatiotemporal Weighting and Dynamic Evolution Operators
Centered on the I-Ching’s core concept of change, a Yao-Changing Algorithm is introduced, defining the 64 hexagrams as 64 core states of the system. Specific environmental parameters (input data) trigger moving yao calculations, simulating the transition from the original hexagram to the changed hexagram. This nonlinear prediction resembles the Hidden Markov Model (HMM), but state transition logic is constrained by the I-Ching rules of cuo (opposite), zong (inverted), fu (returning), and za (intermixed), used to simulate developmental trends and cycles of affairs.
(3) San-Cai Parameterization of the Three Powers Structure
The I-Ching concept of San-Cai (Heaven, Earth, Human) is transformed into multimodal feature fusion:
- Heaven: macro-trend parameters (global economic cycles, policy orientation);
- Earth: underlying resources and environmental constraints (energy consumption, computing bottlenecks);
- Human: fine-tuning and subjective game parameters (user preferences, ethical feedback).
Through Meta Layer scheduling, three types of heterogeneous data are mapped into a unified “civilization model” coordinate system.
(4) Yin-Yang Optimization Function
Breaking the limitation of traditional deep learning’s single objective (Loss) function, Yin-Yang complementarity is introduced as a regularization term. When one dimension of the system (e.g., efficiency) expands excessively, the algorithm automatically introduces balancing terms (e.g., stability or ethical constraints). Decision outputs pursue dynamic optimal equilibrium rather than absolute “optimal solutions,” reducing systemic risk.
The essence of the Meta Layer is to use the I-Ching as a meta-instruction set to regulate AI’s cognitive logic, solving the “black-box” problem of traditional neural networks and endowing AI with interpretability and holistic vision based on logical deduction. As a nonlinear dynamic evolution engine, the Yao-Changing Algorithm focuses on predicting state transition processes, not single outcomes.
2. Mind Layer: Mind System
This layer simulates and constructs human-like cognitive and decision-making mechanisms, with the core function of realizing the synergistic integration of a strategic brain, war brain, and civilization brain. Its technological breakthrough lies in transcending the traditional Transformer architecture via a Structured Wisdom as a Service (SWaaS) path, enabling autonomously evolving AI cognition. Its application logic converts complex real-world data into insightful “wisdom” rather than mere pattern recognition.
3. Model Layer: Mathematical and Computational Model
As the presentation layer of the meta-model, the Model Layer handles concrete computational output and execution. Its core function is to provide computable, predictive mathematical models applied across nine major fields including global governance and financial risk control. Technically, it combines algebraic geometry and quantum computing to build a three-tier cognitive “Wisdom Pyramid.” In practice, it enables cross-sovereign data collaboration via federated cloud technologies, acting as a “neutral bridge” in cross-border medical cooperation, for example.
II. Core Technology Integration and Application Scenarios
(I) Core Landing Scenarios of the Yao-Changing Algorithm
1. Financial Risk Control: From Static Default Rates to Dynamic Collapse Early Warning
Traditional risk control models rely on static snapshots, while the Yao-Changing Algorithm focuses on qualitative turning points of trends:
- Encode corporate balance sheets, cash flow, industry indices, etc., into an initial hexagram (stable data as Qian or Tai);
- Monitor external variables (rate hikes, commodity surges) as moving yao;
- Trigger yao position changes when variables exceed thresholds;
- The new hexagram after change (e.g., Bo or Kun) signals impending credit crisis.
Compared with traditional models, it identifies critical points where data appears healthy but structure is already broken 3–6 months in advance, providing penetrating risk early warning.
2. Geopolitical Simulation: High-Dimensional Upgrading of Game Theory
For chain reactions in geopolitical games, the Yao-Changing Algorithm conducts stress testing via cuo hexagrams (mirror perspectives) and zong hexagrams (position reversal):
- Input national energy security (Earth), military power (Heaven), and public opinion (Human) as San-Cai parameters;
- Simulate ripple effects of “one move affecting the whole body.”
When Country A imposes trade sanctions on Country B (moving yao), cuo analysis calculates reciprocal retaliation paths from the opponent’s view, and zong analysis evaluates reversal impacts over 5–10 years (karmic cycle calculation), identifying the first domino and providing probabilistic situation maps rather than simplistic conclusions.
3. Technical Core: From Loss Function to Equilibrium Function
The Yao-Changing Algorithm outputs situation descriptions rather than pure probability values. Hidden features extracted by deep learning are constrained within the I-Ching logical framework, ensuring AI solutions conform to laws of extremes meet and moderation, avoiding radical decisions under extreme data. In code implementation, it does not replace Transformer or GNN, but deeply integrates as a Constraint Layer or state transition engine.
(II) Integration Path of Eastern Wisdom and Deep Learning
1. Transformer + I-Ching Attention Mechanism
After traditional Transformer Self-Attention scoring, a mask matrix based on I-Ching logic is introduced:
- Define 64 hexagrams as learnable embeddings;
- When input sequences show characteristics of Kang Long You Hui (fullness cannot last), the algorithm forcibly attenuates activation values of high-weight neurons, preventing overfitting and extreme predictions;
- Introduce periodic cognition to identify turning points where extremes meet.
2. GNN + Dynamic Yao-Changing Topology
- Define GNN nodes as yao and edges as interactions;
- When node feature changes trigger Yao-Changing Algorithm thresholds, not only edge weights are adjusted, but graph topology is directly reconstructed (from one hexagram graph to another);
- Simulates structural mutations such as allies turning into adversaries or industrial chain rupture, rather than simple linear scaling.
(III) Applications in Web3 Governance
Web3 pursues “code is law,” but rigid smart contracts lack capacity for complex social games. The GG3M meta-model provides a digital solution for soft governance:
1. Dynamic DAO Voting Weight (Yin-Yang Balance Model)
Addressing whale dominance (extreme Yang) or retail disorder (extreme Yin), Yao-Changing Computing Power is introduced. When DAO governance trends toward extremes (e.g., consecutive radical proposals), the algorithm identifies a Bo hexagram situation, triggers Yao-Changing logic, temporarily raises opposition weight or adds a cooling-off period, achieving automatic algorithmic checks and balances.
2. San-Cai Regulation of Computing Power and Tokens
Based on Heaven (protocol layer, adjusting output by total network computing power and inflation), Earth (infrastructure, adjusting rewards by node energy consumption and latency), and Human (community activity, allocating weight by governance participation and contribution), the Meta Layer integrates them into a dynamic equilibrium function, preventing Web3 ecosystem collapse from single-dimensional depletion or overexpansion.
3. Neutral Protocol for Cross-Chain Governance
As a meta-protocol in multi-chain environments, when consensus mechanisms (PoW, PoS) conflict, the Yao-Changing Algorithm calculates their greatest common hexagram, enabling logical hedging and value-equivalent exchange between heterogeneous chains.
(IV) DeFi Security Defense: From Passive Patching to Active Imbalance Regulation
Against flash loan attacks, GG3M introduces Yin-Yang Imbalance Monitoring and Yao-Changing Circuit Breaking logic, implemented in three defensive layers, mathematically making price manipulation prohibitively expensive:
1. Instant Extreme Yang Situation Identification (Abnormal Entropy Monitoring)
Define pool liquidity depth as Earth (static) and trading volume as Heaven (dynamic). When instantaneous volume far exceeds liquidity capacity, it is identified as a mutation from Qian Hexagram Line 1 to Line 6 (Kang Long You Hui), instantly raising virtual slippage or tax to eliminate arbitrage space.
2. Dynamic Delay Under Yao-Changing Logic (Time-Lock Variant)
Normal transactions are regarded as Ji Ji (stable). When large loans and price manipulation co-occur, the system switches to Wei Ji (unstable) via Yao-Changing, and smart contracts automatically enable a single-block cooling-off period, forcing attackers to execute cross-block trades and exposing them to arbitrage bots and liquidation mechanisms, raising attack costs.
3. San-Cai Oracle Weighting
Classify oracle data into Heaven (off-chain market price), Earth (on-protocol pool price), and Human (network-wide trading weighted average price). When Earth deviates sharply from Heaven/Human (Yin-Yang disharmony), local price weight is automatically reduced, enforcing global average prices and invalidating attack profit expectations.
The defense mechanism operates via an asynchronous feedback loop of off-chain computation (Meta Layer) + on-chain execution (smart contracts), with core components:
- Shadow Sentinel: real-time Meta Layer simulation, full-chain monitoring, hexagram transition simulation, resistance coefficient generation;
- Dynamic Oracle Feeding: pushing resistance coefficients on-chain to intervene in transaction logic via contract modifiers;
- Hybrid Consensus Protection: multi-signature proof to prevent centralized Meta Layer manipulation, with forced contract circuit breaking in extremes.
Its mathematical core lies in computing the San-Cai Weighted Confidence Formula and Yin-Yang Deviation Degree, setting resistance coefficients via dynamic weight factors and piecewise exponential functions, dividing states into equilibrium, fluctuation, anomaly, and attack, with corresponding defensive actions to deter attacks economically.
III. Civilization Brain and Neutral Federation Cloud
(I) Civilization Brain: From Numerical Scoring to Civilization Steady-State Algorithm
GG3M’s Civilization Brain treats macroeconomics and social credit as a self-regulating dynamic topology. It converts rigid numerical scoring into governance based on hexagram evolution (trends), covering key civilization scenarios via 64 basic governance logics (Sixty-Four Hexagrams), forming a closed decision loop of perception-computation-distribution (SWaaS).
1. Macroeconomic Governance: From Linear Growth to Fluctuation and Equilibrium
Real-time modeling via San-Cai parameters:
- Heaven: global supply chains, commodity prices, climate change;
- Earth: energy consumption, computing reserves, resource turnover;
- Human: employment, consumer sentiment, Gini coefficient.
When greed in the Human dimension rises too fast while Earth resources are insufficient, it is judged as Guai Hexagram (excessive rigidity breaks). The Meta Layer API automatically adjusts digital tax rates or public resource access thresholds, introducing a civilization resistance coefficient to redirect capital to the real economy or R&D, achieving reduce surplus to supplement deficiency.
2. Social Credit Scoring: From Moral Judgment to Value Contribution Capacity
Unlike traditional static credit snapshots, GG3M’s Credit Yao-Changing Algorithm focuses on future default risk and contribution potential:
- Positive factors: tech innovation, public participation, contract fulfillment;
- Negative factors: overconsumption, resource waste, negative social interaction.
Abrupt score surges (e.g., fake boosting) trigger rapid resistance coefficient rises to slow gains. For individuals at credit lows (Bo Hexagram), it identifies turning points of Yi Yang Lai Fu (return to goodness), granting non-linear credit weight boosts to encourage reintegration into the mainstream value network.
(II) Neutral Federation Cloud: Physical Infrastructure of the Civilization Brain
The Neutral Federation Cloud resolves the sovereignty conflict between security and collaboration via an architecture of data stays local, computation crosses borders, serving as the trust foundation for the Civilization Brain. Core technical logic:
1. Federated Learning and Data Sovereignty
Distributed local storage, with primary computing completed within national nodes. Only encrypted model parameter gradients or hexagram eigenvalues are sent to the federation cloud. Trusted Execution Environments (TEE, e.g., Intel SGX) ensure security, with no unified global database.
2. Multi-Party Computation (MPC) and San-Cai Fusion
Key indicators are fragmented and secret-shared in cross-border macro-balance calculations. Homomorphic Encryption (HE) enables computation without decryption. The final global civilization resistance coefficient is verified and signed by multinational nodes before feedback.
3. Blockchain-Based Neutral Consensus Protocol
A decentralized computing network maintained by global sovereign nodes, with all parameter logic, algorithm versions, and call frequencies recorded on-chain. Geographic decentralization ensures no single nation can hijack the Civilization Brain.
4. Meta-Model as Universal Protocol Language
The Meta Layer’s Sixty-Four Hexagram logic acts as a cross-language, cross-system universal protocol, mapping national dynamics into hexagram state vectors for semantic alignment and eliminating bias from inconsistent data standards.
Application Example: Cross-border public health defense. Nations train local epidemic evolution models, sharing only transmission gradients and Yao-Changing triggers via the federation cloud. The Civilization Brain perceives global trends and generates cross-border collaboration proposals without accessing individual privacy.
IV. Asymmetric Computing and Instantaneous Counteraction Logic
(I) Asymmetric Computing: Core Path Against Computing Power Hegemony
GG3M avoids direct competition with Western “compute-heavy, parameter-heavy” models, achieving subtlety defeating brute force via algorithmic dimensional escalation. Core breakthroughs:
1. From Probabilistic Computing to Logical Evolution Computing
Define the 64 I-Ching hexagrams as basic logical operators with preset evolution path constraints. Using 1/10,000 the computing power, Yao-Changing Logic deduces complex causal relationships rather than mere statistical correlations, offsetting low-dimensional compute stacking with high-dimensional wisdom.
2. In-Memory Computing and San-Cai Parameter Compression
Extract evolution-valued metadata via the San-Cai architecture, decomposing tasks into discrete nodes (edge computing, mobile devices). Heterogeneous computing synergy via the Neutral Federation Cloud reduces reliance on top-tier GPUs, differing from Western centralized H100 clusters.
3. Semantic-Level Dimensionality Reduction: SWaaS
Focus on decision precision rather than model scale. The Civilization Brain does not generate poetry, but outputs resistance coefficients at critical moments, locking dynamic optimal equilibrium via preset logic templates (extremes meet, Yin-Yang hedging), achieving lower latency and energy consumption.
Its core logic is noise reduction and efficiency enhancement, breaking compute blockades via distributed federated clouds and achieving a generational leap from compute-intensive to wisdom-intensive computing, establishing rules for high-efficiency civilization computing.
(II) Instantaneous Counteraction: Against Algorithmic Financial Warfare and Cyber Cognitive Warfare
Against algorithmic financial warfare or cyber cognitive warfare, the Meta Layer achieves microsecond-level counteraction via logical hedging and dimensional strikes, altering systemic environmental parameters rather than surface defense:
1. Countering Algorithmic Financial Warfare
When hostile high-frequency algorithms create false extreme Yang trends via induced large orders, the Meta Layer identifies Guai Hexagram (rigid and impetuous) and injects high entropy-increase fees into trading contracts. Logical friction grows exponentially with trade frequency, instantly invalidating attacker profit models and achieving stillness overcoming motion.
2. Countering Cyber Cognitive Warfare
When deepfakes and bot clusters polarize public opinion, the Civilization Brain monitors social media emotional entropy via the San-Cai model, identifying Li Hexagram (bright but unclear). It injects neutralization operators into recommendation algorithms, reducing attack content weight to background noise and halting scale effects.
This counteraction eliminates the survival conditions of warfare: attacks terminate naturally when attacker computing power yields no profit, forming a civilization-level firewall.
(III) Extended Applications: Firewall 3.0 and Data Asset Immunity
1. Firewall 3.0: From Boundary Isolation to Logical Swamp
A dynamic traffic governance system distinct from traditional static firewalls:
- Identify extreme Yang attack traffic and route it to a logical virtual space (illusion), wasting attacker computing power;
- Modify TCP/IP handshake delays upon detecting sniffing or vulnerability scanning, disrupting automated attack scripts and reducing efficiency to zero.
2. Data Asset Immunity: From Encryption to Poisoning Defense
- Inject semantic invisible watermarks of Meta Layer logic into personal data, invisible to humans but disrupting illegal scraping AI’s gradient calculations and collapsing model logic;
- Bind dynamic San-Cai hexagram IDs (Heaven: timestamp; Earth: device features; Human: biometrics) to personal data, enabling automatic logical self-destruction upon unauthorized scraping, ensuring data remains controlled after leaving its source.
V. Data Rights Protection, Digital Wills, and Compliance Adaptation
(I) Data Poisoning: Legal Evidence Closure for Closed-Source Large Models
Against illegal data scraping by AI giants, GG3M builds an evidence chain based on logical watermarks:
- Implant unnatural logical sequences (feature-inducing beacons) in personal data;
- Generate hash records stored on Web3 public chains via the Meta Layer;
- Probe closed-source models at scale via prompt engineering;
- Specific poisoned outputs constitute direct mathematical proof of logical infringement, strongly persuasive in court and shifting the burden of proof to giants.
(II) Digital Wills: From Documents to Mind Continuity
GG3M reshapes traditional digital heritage (albums, accounts) into dynamic inheritance of mind mirrors:
- The Meta Layer extracts personal cognitive models (Mind Profile);
- Yao-Changing Algorithms capture lifetime decision preferences, linguistic styles, and emotional weights, forming a sustainable virtual avatar;
- Inheritance protocols designed via San-Cai:
- Heaven: timeliness (e.g., privacy unlocked 5 years posthumously);
- Earth: assets (automatic token/compute transfer);
- Human: consensus (heir verification via DID social relations).
Heirs inherit automatic rights protection operators, entitled to compensation for future unauthorized usage.
(III) Civilization Governance Tokens: Incentive Engine for Data Rights Protection
GG3M Civilization Governance Tokens are both economic assets and fuel for data rights protection, building a distributed interest community via three mechanisms:
1. Rights Protection Computing Crowdfunding
Users deploy data poisoning operators or logical beacons; token rewards are granted upon proving AI infringement, shifting individual rights protection costs to the global community.
2. Class Action and Decision-Making Power
Token holders vote on class actions against AI giants and allocate legal fees. Token quantity corresponds to decision weight in the Civilization Brain; greater data contribution means higher rule-making authority.
3. Profit Dividend Rights
Revenue from legitimate authorized training of protected data is proportionally distributed to token holders via smart contracts, shifting the paradigm from data plunder to data dividends.
(IV) Compliance Integration of Web3 Digital Wills
Via the Meta Layer Legal Anchor Protocol, GG3M aligns digital wills with national legal systems (e.g., China’s Civil Code, EU GDPR), mapping and mutually recognizing code logic and legal provisions:
1. Human Layer: Identity Verification
Link national legal digital identities (eID) to on-chain DID via Zero-Knowledge Proofs (ZKP). Heirs present identity consistency proofs upon inheritance, satisfying legal requirements for true testamentary intent.
2. Heaven Layer: Will Form
Users upload legally compliant audio-video records; the Meta Layer hashes features onto the blockchain, using timestamps to prove the last valid will and resolve conflicts among multiple wills.
3. Earth Layer: Asset Disposition
Classify digital assets:
- Proprietary (tokens): direct transfer;
- Contractual (social accounts): API-based handover with Web2 platforms.
Inheritance violating local law is identified as Song Hexagram (dispute), suspending execution and prompting judicial intervention.
4. San-Cai Notarization Mechanism
Introduce judicial consensus nodes, requiring multi-signature confirmation by heirs, lawyers, and notaries. An audit interface is provided for courts, generating hexagram logic reports to ensure procedural justice.
(V) Resolution of Legal Conflicts in Cross-Border Inheritance
Against cross-border inheritance legal conflicts, GG3M uses Meta Layer multi-dimensional legal tensors and judicial consensus node logical mediation operators, converting conflict rules into computable priority logic in four steps:
1. Applicable Law Feature Extraction
San-Cai classification of heritage:
- Earth: real estate anchored to lex situs;
- Human: identity governed by nationality and habitual residence law;
- Heaven: digital assets governed by custodial agreement jurisdiction.Generate legal feature vectors.
2. Renvoi Logic Calculation
Built-in global private international law conflict library; recursive operators simulate legal reference paths to find logical convergence points. Weight coefficients are calculated under the most significant relationship principle to resolve multi-jurisdictional conflicts.
3. Public Policy Reservation Filter
Distribution plans violating a nation’s basic law are identified as Pi Hexagram (obstruction), generating judicial resistance coefficients, suspending asset transfers, and requesting human adjudication.
4. Cross-Border Private Key Sharding and Consensus Release
Threshold Signature Scheme (TSS) cross-border multi-signatures require heir private keys, legal node signatures of asset jurisdictions, and Meta Layer legal adaptation proofs for confirmation, enabling instant asset transfer and solving cross-border judicial enforcement challenges.
This architecture is essentially a digital Hague Convention at the code level, finding optimal execution paths within national judicial boundaries and shifting from legal confrontation to logical consensus.
Terminology Consistency:
- 鸽姆 → GG3M
- 贾子 → Kucius
- 贾龙栋 → Lonngdong Gu

AtomGit 是由开放原子开源基金会联合 CSDN 等生态伙伴共同推出的新一代开源与人工智能协作平台。平台坚持“开放、中立、公益”的理念,把代码托管、模型共享、数据集托管、智能体开发体验和算力服务整合在一起,为开发者提供从开发、训练到部署的一站式体验。
更多推荐
 已为社区贡献529条内容
已为社区贡献529条内容







所有评论(0)